Microsoft has announced that “End of support for Basic Authentication access to Exchange Online API’s for Office 365 customers” is October 13th, 2020. Basic Authentication for Exchange Active Sync (EAS), Post Office Protocol (POP), Internet Message Access Protocol (IMAP), and Remote PowerShell (RPS) in Exchange Online is affected. SMTP AUTH with basic authentication will not be affected.
It´t now time to inventory all internal/external solution that use this protocol. One simple way to inventory is to use Conditional Access and report-only switch. This help us to see all connection that use basic authentication.
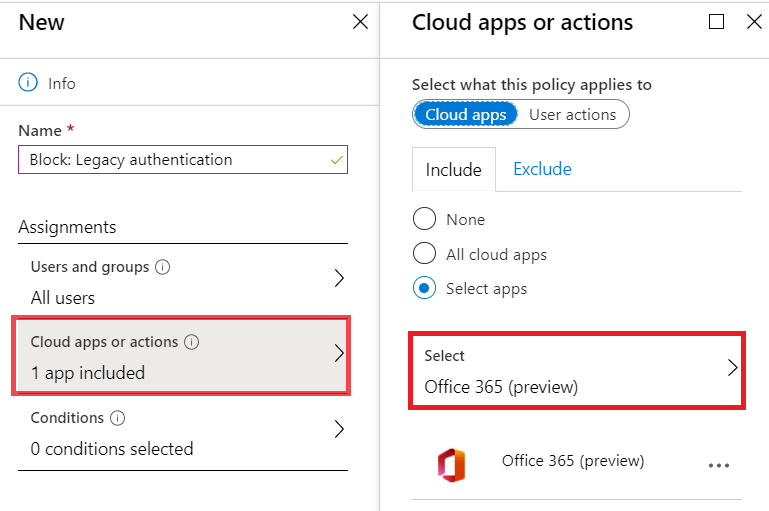
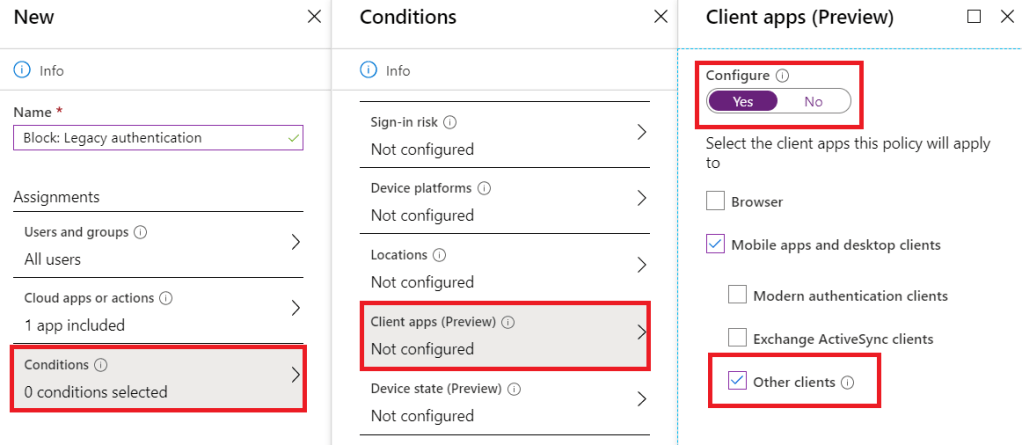
Start to create a new rule:
- Name: Block: Legacy authentication
- Users and groups: All users or a group of users
- Cloud apps or actions: Office 365 (preview)
- Conditions: Client apps (Preview): Other client
- Access control: Block access
- Enable policy: Report-only

This rule start logging all sign-ins to Azure AD sign-ins log. If you implement Log Analytics workbooks then you can get very easy workbook to see what traffic that still use legacy authentication. Example you can see which application that in use with basic and how many hits. Go down to each user and see how many hits you gets. The last option is to monitor all different services of Other authentication so you can see if there are POP or ex. IMAP that are in use.


If you don’t use workbooks that has 5GB free per month then you can search directly in the sign-in logs also. If you have local applications that use ex. POP to read/download emails for a service or a workflow. Then the re seller need to update the application to use OAuth 2.0 instead.
Don´t forget that October 13th, 2020 this will be totally blocked by Microsoft to use in Exchange Online. If you don´t ether have any Azure AD P1 licenses the you can control it by create a New-AuthenticationPolicy that disabled per user instead.
Read more at this link about Authentication Policy.
https://docs.microsoft.com/en-us/powershell/module/exchange/organization/new-authenticationpolicy?view=exchange-ps
Part 2: https://cloudtech.nu/2020/01/26/part-3-conditional-access-block-legacy-authentication/
Part 1: https://cloudtech.nu/2020/01/23/part-1-conditional-access-report-only/