In Azure there are a lot of Single Sign-On (SSO) options. Many early adopters in cloud use ADFS based on that SSO was not a part of AD Connect at the beginning. Today we have more than one solution to choose between.
Active Directory Federation Services (ADFS)
This is an on-premies solution that is important if you need to move the sign-in to local Active Directory. You can do it with PTA today also witch is a part of AD Connect configuration. Another need to use ADFS today is smartcards but it will come to Azure AD in the future.
Seamless Single-Sign On
Works with all Windows 7 and above. The solution is built on local AD joined computers that are signed in to the domain on local network. Some web-sites appear with SSO and Office packages activates with this function.
Azure AD Hybrid Join (PRT token)
This is the solution to use today if you run Windows 10. It works with downgrade computers like Windows 7, 8 and 8.1 with a client installed. You can sign-in from the computer everywhere and get SSO. We will cover this setup later.
Workplace Join (AD registration)
Primary audience is bring your own device (BYOD). If you not run Azure AD Hybrid Join or sign-in from a computer in workgroup you asked for AD registration. The user store the computer account in Azure to get SSO to Office 365. In enterprise environment this is not a solution you want to use. From Windows 10 1803 you can block this function in enterprise environment and replace with Azure AD Hybrid Join.
Azure AD Joined
The computer is connected to Azure AD directly and get SSO to Office 365/Azure.
My personal recommendations today is to configure AD Connect SSO together with Azure AD Hybrid Join. SSO works with all downgrades and Azure AD Hybrid Join with native Windows 10.
Configure Azure AD Seamless Single-Sign On
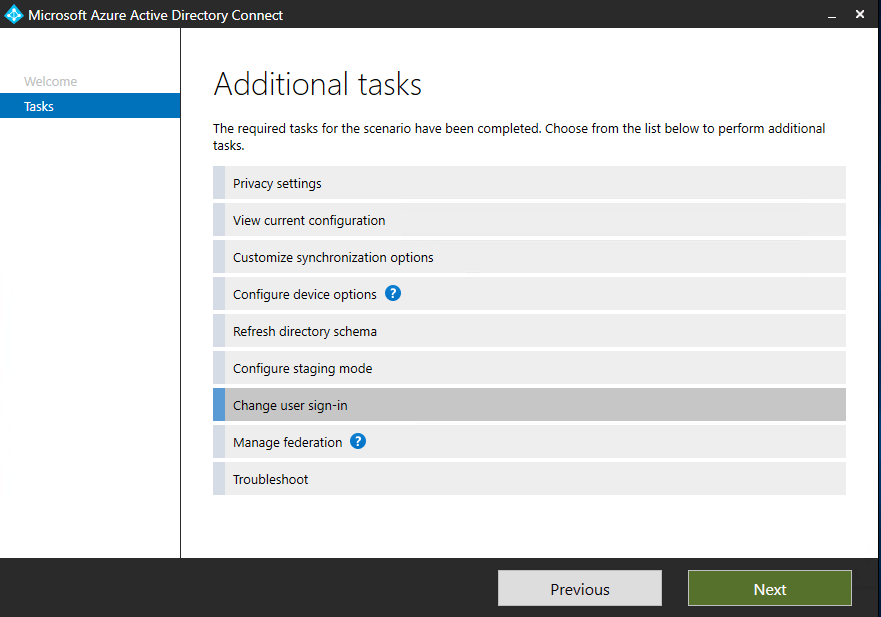
Start to configure Seamless Single sign-on in AD Connect Wizard. Change user sign-in
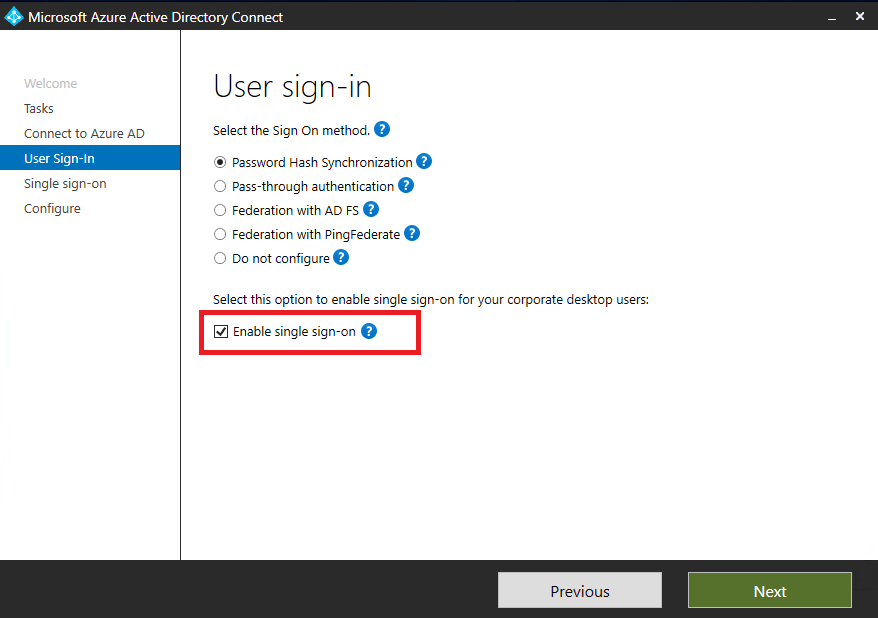
Enable Single Sign-On, Next, Sign-in with local domain credentials. AD Connect is now ready to enabled computers with SSO but all users need to update intranet zone to get this function to work. The setup create a computer account (AZUREADSSOACC) in each AD forest.
Add endpoints to Intranet Zone
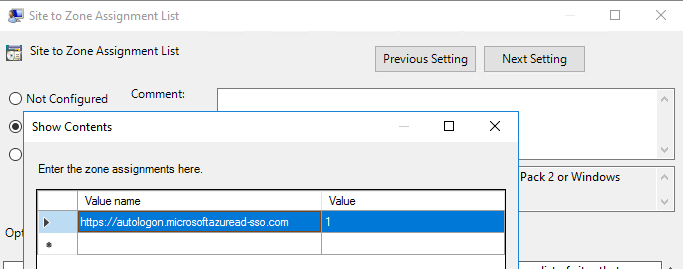
The following URL need to be explicitly added to the machine’s Intranet Zone. This settings makes sure that the browser sends the currently logged in user’s credentials in the form of Kerberos ticket to Azure AD.
Best way to do this is to create a GPO:
- Create a GPO that’s applied to all users or add it to an existing Internet Explorer settings GPO
- Go to User Configuration\Administrative Templates\Windows Components\Internet Explorer\Internet Control Panel\Security Page and select Site to Zone Assignment List
- Enable to policy and add the following values:
Read more about the configuration in Microsoft doc.
https://docs.microsoft.com/en-us/azure/active-directory/hybrid/how-to-connect-sso-quick-start
Block Workplace Join
In 1803 and above releases, the following changes have been made to avoid this dual state. This is very important in all environment. Before any migration between tenants it´s recommended to upgrade Windows 10 to at minimum 1803 to support removal of dual state.
HKLM\SOFTWARE\Policies\Microsoft\Windows\WorkplaceJoin, “BlockAADWorkplaceJoin”=dword:00000001
In next blog you can read more about to setup Azure AD Hybrid Join (PRT token) https://cloudtech.nu/2020/03/09/configure-hybrid-azure-ad-joined-with-ad-connect/