Finally Microsoft release the public preview of Temporary Access Pass. Why is that so important?
For all Firstline workers without mobile device it´s hard to configure MFA (Multi Factor Authentication). They need assistance from an IT support to setup FIDO2 security key. With TAP (Temporary Access Pass) it´s now possible to configure a passcode for new users to sign in and register MFA without need of SMS or Microsoft Authenticator already configured.
There are som limitation to get it to work.
- Users in scope for Self Service Password Reset (SSPR) registration policy will be required to register one of the SSPR methods after they have signed in with TAP. If the user is only going to use FIDO2 key, exclude them from the SSPR policy or disable the SSPR registration policy.
- Do not require of MFA by Conditional Access or Identity Protection settings. Exclude by trusted device or network.
- Registration of FIDO2 security keys needs to be completed within 10 minutes after the first sing-in
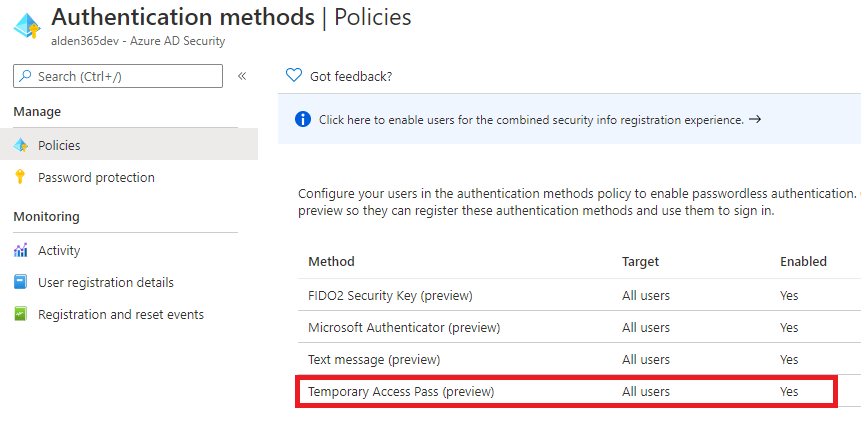
Enable the TAP policy
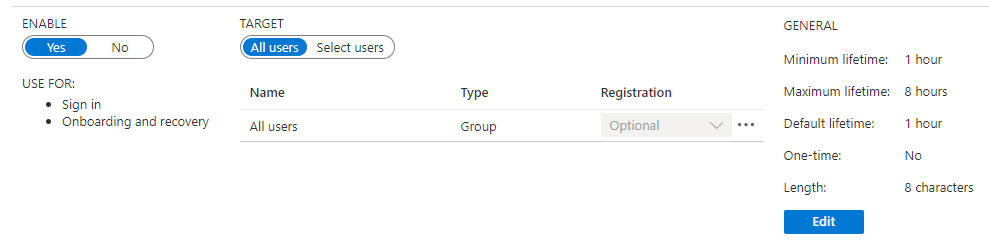
Begin to create a TAP policy in Azure AD portal. Enabled the Temporary Access Pass (preview) by select the target to All users or a group of users to pilot the function. There are also a setting to configure the lifetime.
Authentication methods – Microsoft Azure
Create a TAP for the user
That’s all to start use the TAP service for end user account. To create a TAP code you need following permissions.
- Global administrator
- Privileged Authentication administrator
- Authentication administrator
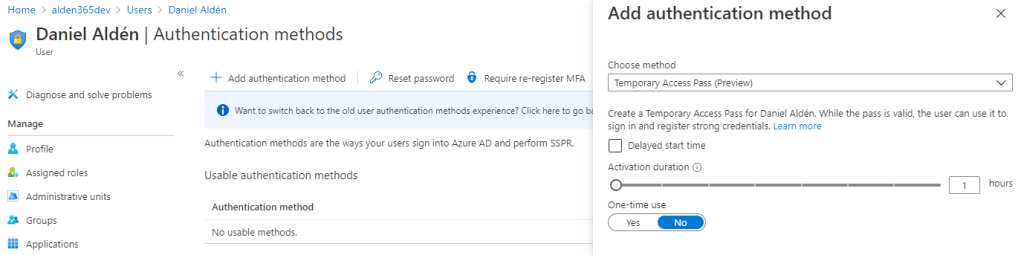
Click Azure Active Directory, browse to Users, select a user, such as Daniel Aldén, then choose Authentication methods.
Ensure that you enable the “new user authentication methods experience“. Add authentication method. Select Temporary Access Pass (preview) and select for how long time the user activation is enabled. The “Activation duration” depends on which lifetime settings where made earlier.
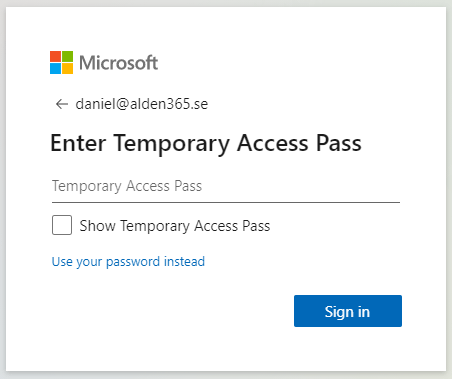
When the code is active you will be prompted to sign in with TAP code next sign-in.
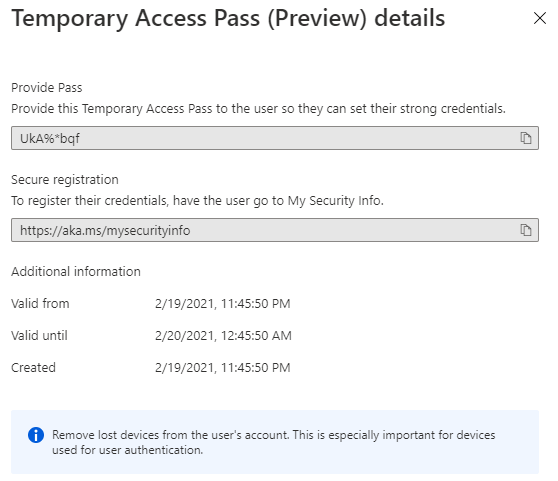
Open a browser and use this link https://mysignins.microsoft.com/ to setup the user MFA setting with FIDO2 security key.
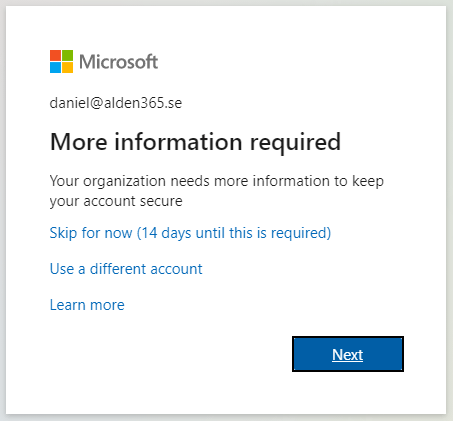
If you get this prompt then the setup will failed. Go back and exclude the user from Conditional Access rules.
If you click next you didn’t got the prompt to register FIDO2 security key. Even if you click “Skip for now (14 days until this is required)” you will be prompted to register MFA again before save the FIDO2 security key.
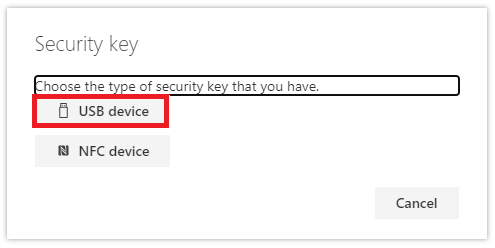
Click Add method. Select Security key.

Select USB device
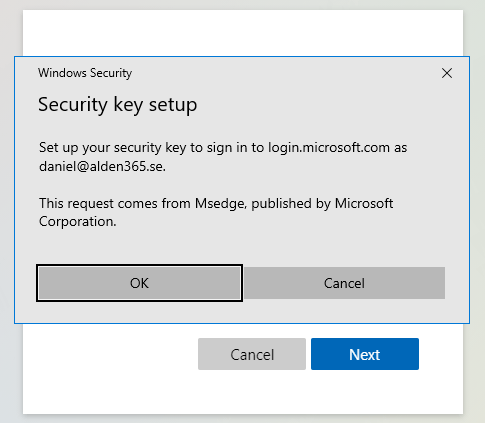
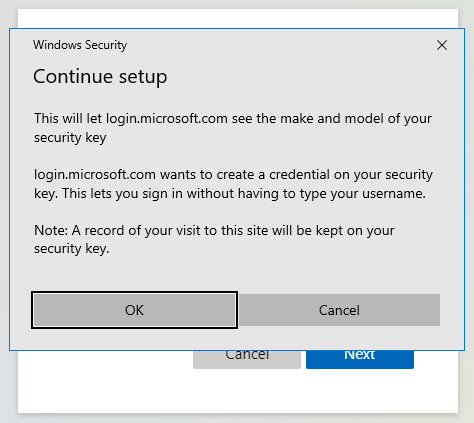
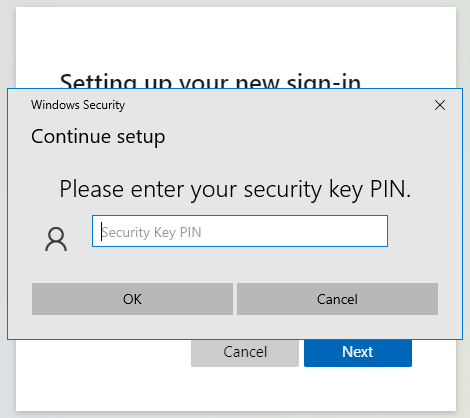
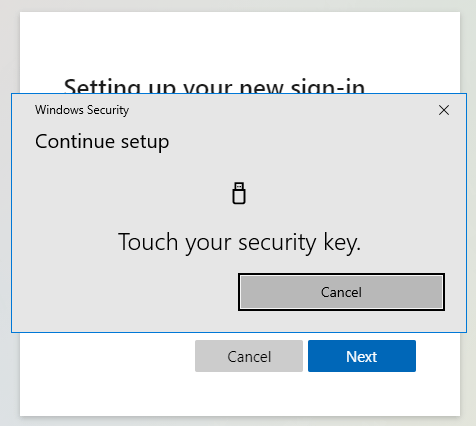
Click Next, OK, OK and then enter the PIN of security key.
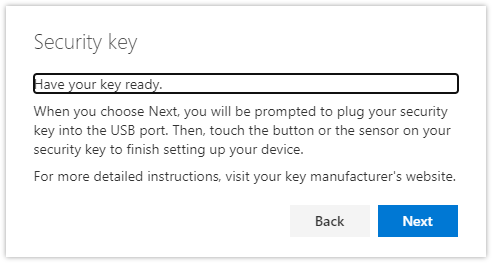
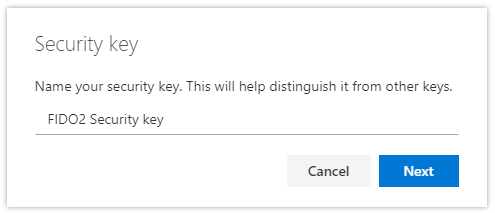
Enter the name of the key that are listed in mysign-ins.
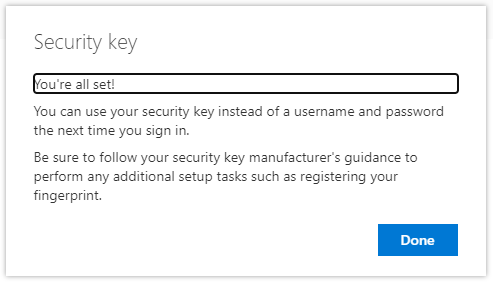
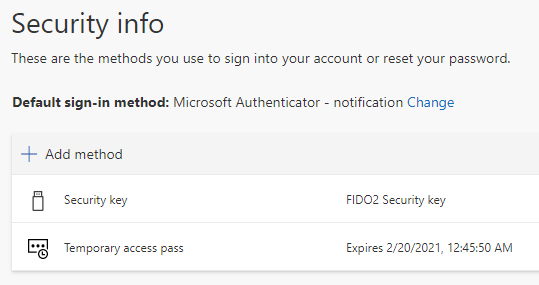
Now the account is ready to use the security key to sign-in to Microsoft 365 services. Don´t forget to enable the MFA requirement for the user if you don´t sign-in from trusted PC which is recommended instead of excluding the user from MFA.
Read more in Microsoft Doc
Configure a Temporary Access Pass in Azure AD to register Passwordless authentication methods | Microsoft Docs